Sailpoint IdentityIQ
This is the procedure to integrate inWebo multi factor authentication service with "Sailpoint IdentityIQ" authentication solution.
InWebo provides software 2-factor authentication technologies with a « chip & PIN » security level. InWebo tokens can be used on any device (desktop, tablet, smartphone, etc.), without any expertise and in a self-service mode. InWebo offers a highly available trusted platform, built with Hardware Security Modules (HSM), compatible with your Identity Management systems, which you can implement in SaaS mode, in a matter of hours, with no new infrastructure or investment.
The purpose of this guide is to explain how to use InWebo products with IdentityIQ .
General Principles
InWebo strong authentication service supports many built-in interfaces such as Radius, SAML 2.0, Web Services API, Google Apps and many more. When working with a network device (firewall, reverse proxy,…) the preferred method is RADIUS. This is what we will explain further in this document.
Architecture is described below:
Users can download and manage InWebo tokens by themselves. In order to get the whole system up and running, your company system administrator only has to:
Configure IdentityIQ authentication portal with SAML (10 min)
Create an InWebo account (2 min)
Download, install and activate one of InWebo tokens (4 min)
Configure a SAML connector in his InWebo account (2 min)
Perform a test authentication (1 min)
Basically, the whole system can be up and running in 15-20 minutes.
Configuring inWebo SAML authentication on Sailpoint IdentityIQ
1. Configuring the inWebo SAML IdP connector
As it's easier to create the IdP connector from IdP metadata, you first need to add a SAML connector on the InWebo IdP part.
Connect to the InWebo administration console https://www.myinwebo.com/console
Click on the “Secure Sites” tab
Add a “SAML 2.0” connector by choosing in the drop-down list of the “connectors” section.
Optional : give it a name, 'SailPoint IIQ SAML 2.0' by example
Leave SP Metadata field blank for the moment
Validate by pressing the “Add” button.
A successful message updates the windows as well as the new generated IdP Metadata.
Click the “Download inWebo IdP SAML 2.0 metadata in XML format” link to download them on your computer.
Click the “Download inWebo IdP SAML 2.0 certificate” link to download the certificate on your computer. It will be used to encrypt SAML assertions.
Keep your browser opened on this SAML connector as we will need to copy-paste some of the informations in the next step below.
2. Configuring the SailPoint SAML SP service
Now connect to your IdentityIQ administration interface in a new browser window.
We have to configure a SAML IdP connector so that Sailpoint IdentityIQ (as a SAML service provider) can send authentication requests to this IdP (inWebo), relying on it to authenticate users and to provide access to resources behind.
Note: these following URLs need to be adapted based on your environment. For your own configuration, the actual URLs are provided in the inWebo web admin console in the SAML v2 connector popup or in the Metadate file available from the inWebo web admin console.
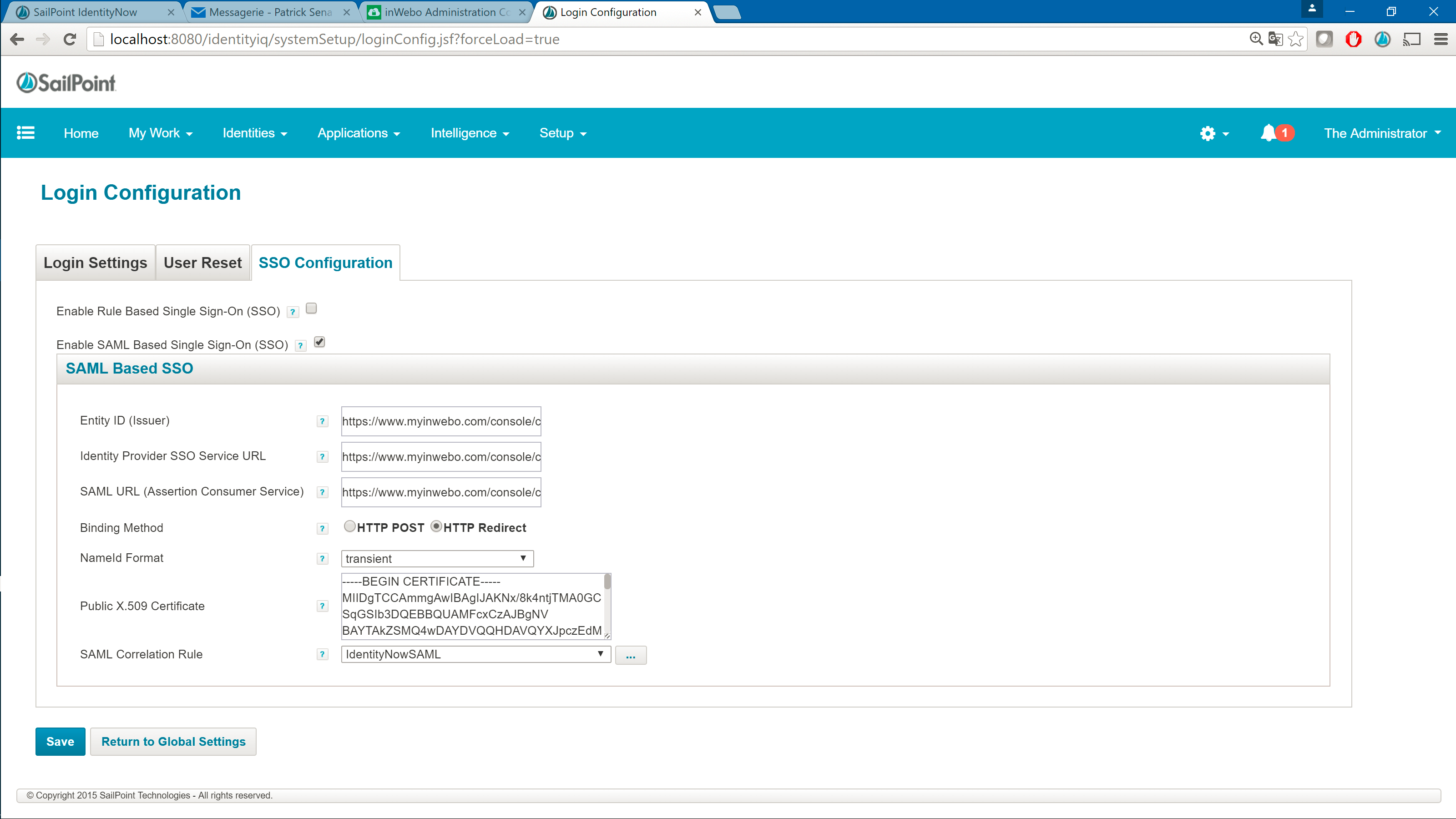
Go to Global Settings > Login Configuration > SSO Configuration > Enable SAML Based Single Sign-On (SSO)
Entity ID (Issuer) is based on the Metadata from the inWebo web admin console: https://www.myinwebo.com/console/c/<ServiceID>/saml2/<ConnectorID>/metadata (= 'Issuer URL' in the inWebo SAML connector)
Identity Provider SSO Service URL : https://www.myinwebo.com/console/c/<ServiceID>/saml2/<ConnectorID> ( = 'Single Sign On URL' in the inWebo SAML connector)
SAML URL (Assertion Consumer Service) : https://www.myinwebo.com/console/c/<ServiceID>/saml2/<ConnectorID> ( = same as above)
Public X.509 Certificate : open the certificate downloaded from the inWebo web admin console with a text editor and copy-paste its content here.
SAML Correlation Rule : use the default seri one
XML// Imports import sailpoint.object.Identity; // Making a BIG assumption here that the nameid-format is unspecified/persitent // Get the nameId from the assertionAttributes String nameId = (String)assertionAttributes.get("nameId"); Identity ident; if(nameId != null) { // Lookup the identity based on nameId ident = context.getObject(Identity.class, nameId); } return ident;
You configuration should now look like this :
Click on save.
3. Exporting SAML SP metadata from IdentityIQ to inWebo
You need to convey the SP metadata from IdentityIQ to the InWebo SAML IdP that provides authentication service to this SP. Exporting the SAML SP metadata to a file provides you with the information that you need to do this.
download the IdentityIQ SAML metadata in a text file.
You now have to use the information in the download XML file to fill the SP metadata on the InWebo IdP SAML Connector.
open the donwloaded XML metadata in a text editor and copy the entire content of that file in the clipboard of your computer (CTRL+C most of the time under Windows systems).
Back to your inWebo administration console (https://www.myinwebo.com/console), click on the “Secure Sites” tab.
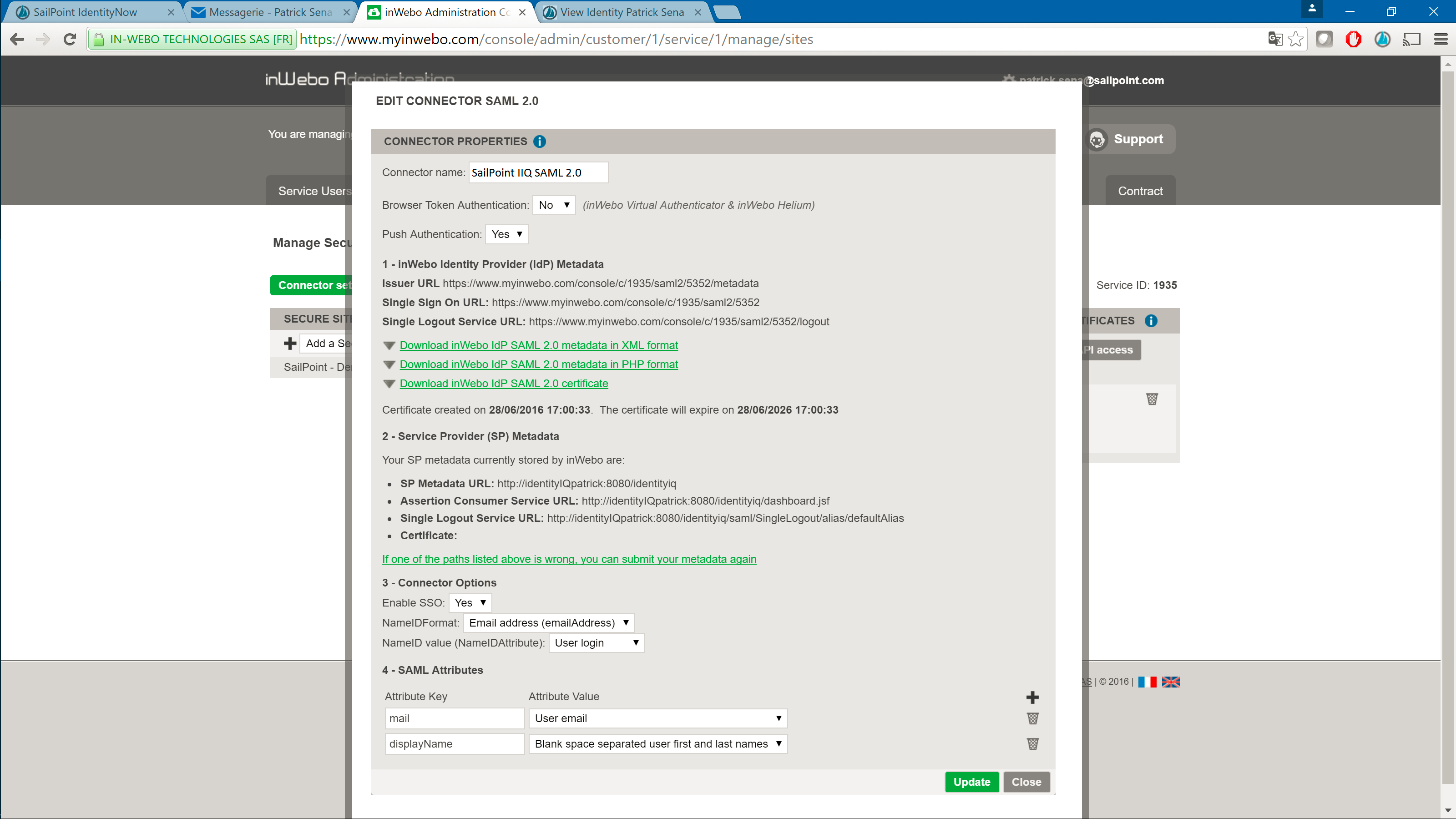
Edit the previously added “SailPoint SAML 2.0” connector by clicking the pen icon on the right of the connector name in the “connectors” section.
Paste the Metadata from the clipboard (CTRL+V most of the time under Windows systems) in the Metadata Service Provider (SP) section of the opened window.
Clic in 'Connector Options', and select 'Enable SSO' = 'Yes'
Set 'NameIDFormat' = 'Email address (emailAddress)'
Set 'NameID value (NameIDAttribute)' = 'User login'
The leave the last section 'SAML Attributes' as is.
Validate by clicking the Update button, then close the window with the Cancel button.
Your Saml connector should now look like this :
4. Test your integration
Type the IdentityIQ Login page URL to test it.
You now should be redirected on an inWebo authentication page, that displays Virtual Authenticator if your current web browser is enrolled as a device in inWebo.
If your current browser is not enrolled, you are prompted to enter your login in the field to authenticate using you mobile phone. It must prior have been enrolled.
