This is the procedure to integrate inWebo multi factor authentication service with "CyberArk" authentication solution.
Prerequisites
-
To install inWebo CyberArk SAML connector you'll need the CyberArk API version 9.8. or higher.
-
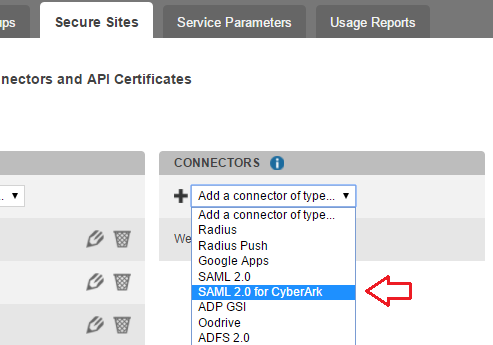
This is not a standard feature so you have to contact the inWebo team to activate the CyberArk SAML connector for your service.
Installation
-
It will allow you to add the "SAML 2.0 for CyberArk" in the console
Configuration
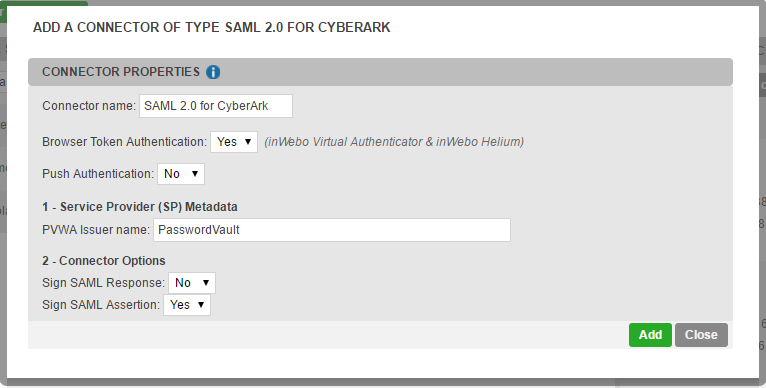
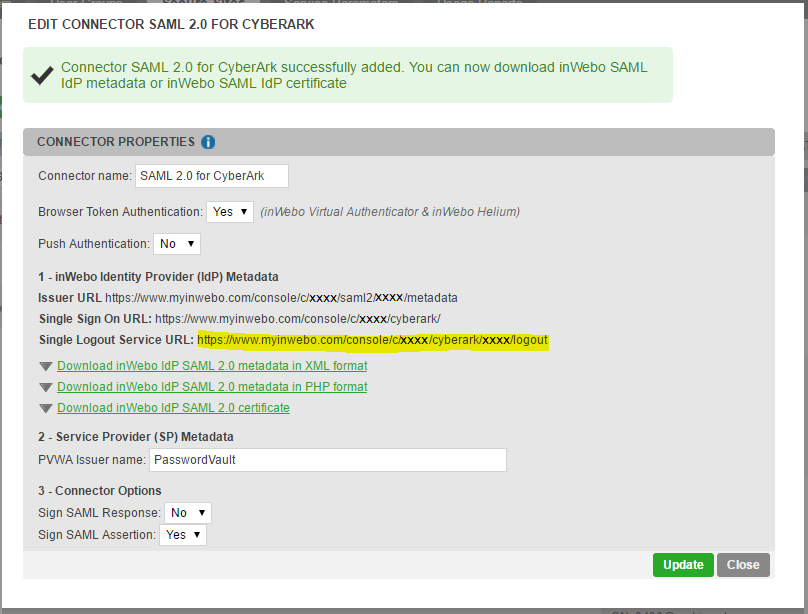
The connector
-
The configuration is minimal and most of the time you don't have to modify the default settings
After you finish setting up the SAML 2.0 connector you'll have the possibility to add a new type of secure site
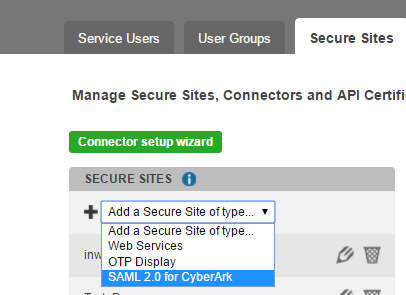
The secure site
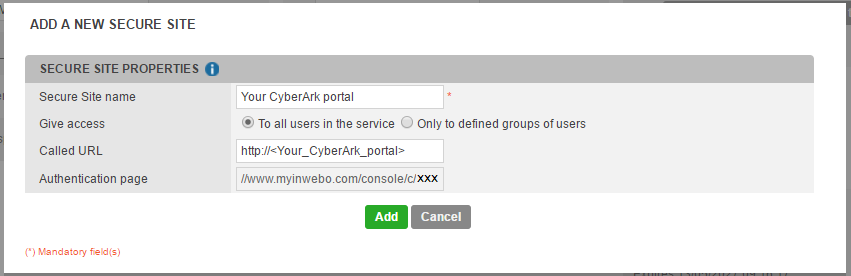
-
In the SAML 2.0 CyberArk secure site, you just have to add the URL of your CyberArk portal in the "Called URL" field
Configuring CyberArk Password Vault Web Access system (PVWA)
Now you have to add inWebo as SAML authentication provider in CyberArk PVWA.
Configuring Administration / Options / Authentication Methods
-
Log onto the PVWA as the predefined Administrator user.
-
Click ADMINISTRATION to display the System Configuration page, then click OPTIONS;
The main system configuration editor appears. -
Expand Authentication Methods; a list of the supported configuration methods is displayed.
-
Select saml and make sure the Enabled property is set to Yes.
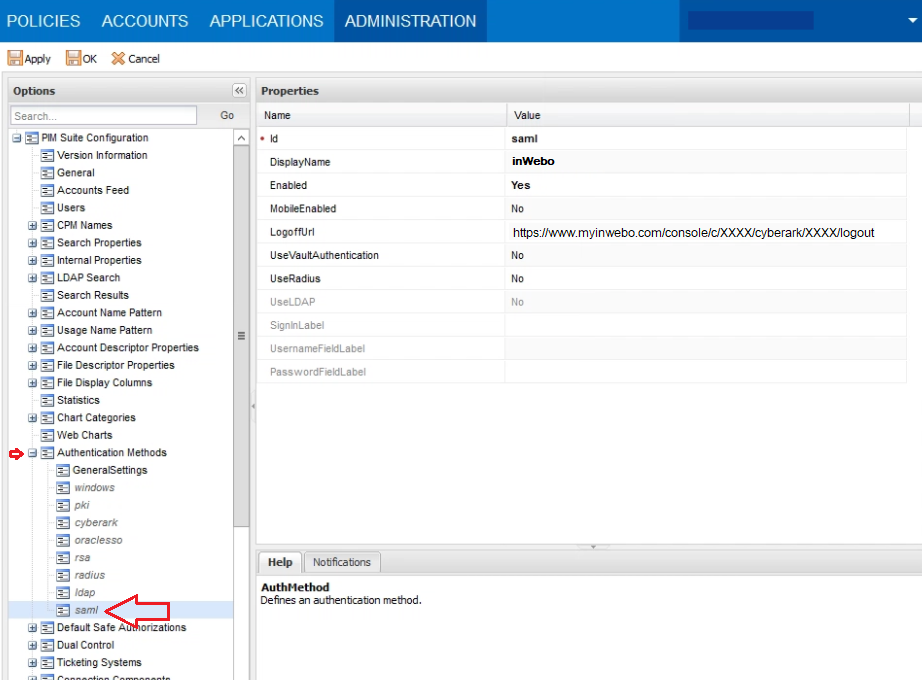
-
In LogoffUrl, specify the logoff page of your IdP.
This LogoffURL is the Single Logout Service URL you can find in the settings of your SAML 2.0 CyrberArk connector
Click Apply to save the new configurations and stay in the Options page
Configuring Administration / Options / Access Restriction
In the Options page,
-
Right-click Access Restriction,
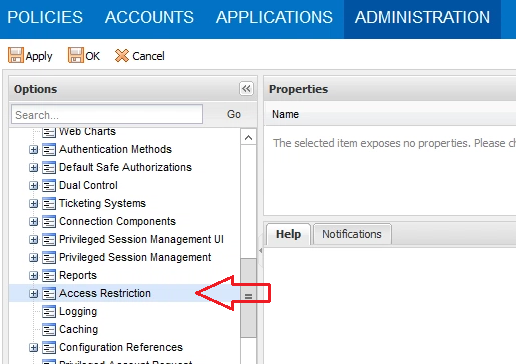
-
Then select "Add AllowedReferrer"; a new parameter node is added to enable you to configure an Allowed Referrer.
-
In the Allowed Referrer property list, in BaseURL, specify the inWebo URL:
https://www.myinwebo.com -
Click Apply to save the new configurations.
File modifications to enable MFA on CyberArk
To enable MFA on CyberArk you need to modify the “web.config” file and for CyberArk 11.6 and later you have to modify also the “saml.config” file. All the information needed to configure these two files is available in the inWebo connector window.
Updating the Web.config file
In the PasswordVault web.config file:
-
In the PasswordVault installation folder, open the web.config file.
-
In the appSettings tag, add the following parameters:
-
IdentityProviderLoginURL – The login URL of your IdP.
You can find it in the parameters of your SAML 2.0 CyberArk connector :
"Single Sign On URL: https://www.myinwebo.com/console/c/XXXX/cyberark/XXXX" -
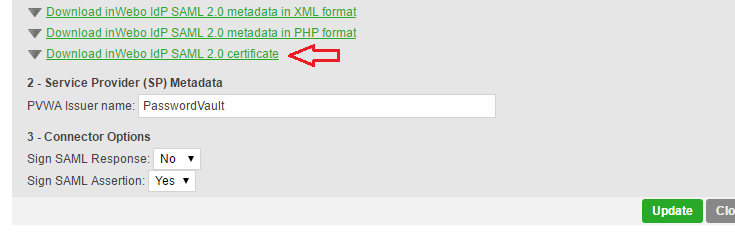
IdentityProviderCertificate – Download the required SAML 2.0 certificate file in the SAML 2.0 for CyberArk connector parameters
-
Issuer – The Issuer string that enables the PVWA to identify itself to the IdP. This value must correlate to the value used by the IdP to identify PVWA as a relying party. The default value for this parameter is PasswordVault.
Sample of web.config file lines to be modified:
<add key="IdentityProviderLoginURL" value="https://www.myinwebo.com/console/c/XXXX/cyberark/XXXX" />
<add key="IdentityProviderCertificate" value="~~~~~Paste Full certificate as a one line character string here~~~~~" />
<add key="Issuer" value="PasswordVault" />
Updating the saml.config file (only for CyberArk 11.6 and later)
If you are already working with SAML authentication, and you are upgrading to 11.6 or later, you need to update your SAML configuration settings.
Open the saml.config file located in the installation folder (the default location is \Inetpub\wwwroot\PasswordVault), and change the following elements:
-
ServiceProvider Name = "PasswordVault"
-
Description = "PasswordVault Service Provider"
-
PartnerIdentityProvider Name = "https://www.myinwebo.com/console/c/***SID****/saml2/**ID**/metadata"
-
SingleSignOnServiceUrl = "https://www.myinwebo.com/console/c/***SID****/cyberark/**ID**"
-
Certificate String = "<< certificate string >>
All these elements can be found in your inWebo CyberArk Connector:
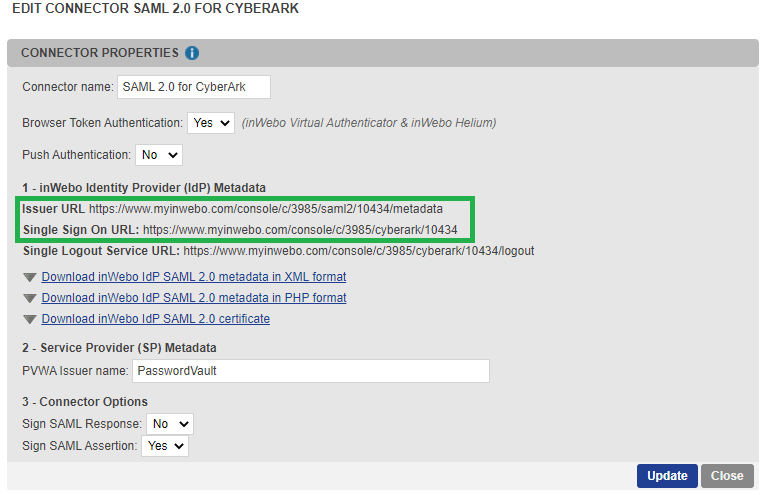
-
PartnerIdentityProvider Name = Issuer URL
-
SingleSignOnServiceUrl = Single Sign On URL
-
Certificate String = "InWebo IdP SAML 2.0 certificate", you can download it in .crt, edit the text and select all but without the string "-----BEGIN CERTIFICATE-----” and “-----END CERTIFICATE-----”
